CBM-BASIC: Commodore BASIC–style interpreter written in C
The article provides an overview of CBM BASIC, a version of the BASIC programming language developed for the Commodore PET computer in the late 1970s. It discusses the features and capabilities of CBM BASIC, as well as its historical significance and influence on personal computing.
A collaborative pixel mural where each 16×16 tile is owned and editable
NFTMural.io is an online platform that allows users to create and share digital murals made up of unique NFT (non-fungible token) art pieces. The platform aims to foster a collaborative community of digital artists and enthusiasts who can build and explore immersive virtual murals.
X11 user daemon to automatically run commands triggered by user specified events
Nvidia Built the A.I. Era. Now It Has to Defend It
Show HN: MUP – Interactive UI inside LLM chat, so anyone can use agentic AI
Agentic AI is powerful, but most people never experience it — it's trapped behind text commands and dev tools.
MUP (Model UI Protocol) lets you embed interactive UI directly in LLM chat. Each MUP is just a single .html file. The same functions can be triggered by the user (clicking a button) or by the LLM (function call). Both sides see each other's actions in real time.
The repo includes a PoC host and 9 example MUPs. Demo mode lets you interact with the UI side without an API key. Add an OpenAI key to see full LLM-UI collaboration.
Demo videos in the README show things like: drawing pixel art then charting its colors, a camera that captures a scene and the LLM recreates it, making beats on a drum machine with the LLM.
I'd love feedback on the protocol design.
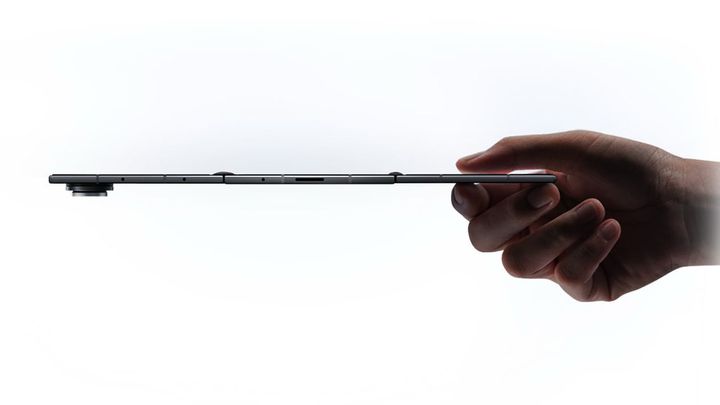
Samsung to Discontinue Galaxy Z TriFold After Just Three Months
Samsung is reportedly planning to discontinue its Galaxy Z Trifold smartphone, a foldable device with a unique triple-fold design. The decision is said to be driven by the device's limited market appeal and sales performance.
VEO – Open-source content-adaptive video encoding optimizer in Go
Veo is an open-source, lightweight, and highly configurable virtual environment orchestrator that simplifies the management of containerized applications. It provides a user-friendly interface and a set of powerful features to deploy, manage, and monitor multi-service applications in a cloud-agnostic manner.
Trapped Inside a Self-Driving Car During an Anti-Robot Attack
Java 26 Released

The first open-source agentic AI physicist
Quickly Get Your Local and Public IP Address from the Command Line
The article provides a simple way to quickly retrieve your local and public IP addresses from the command line, using a combination of built-in and third-party tools. It offers step-by-step instructions for Linux, macOS, and Windows systems.
Nvidia making AI module for outer space
Nvidia has developed an AI module designed for space applications, capable of processing large amounts of data and performing complex machine learning tasks while consuming minimal power. The module is aimed at enabling advanced space exploration and satellite missions by providing powerful on-board AI capabilities.
Voice‑First‑Messages. Perfected.
Haiket is a website that provides news, analysis, and commentary on technology, business, and innovation. The site covers a wide range of topics, including emerging technologies, industry trends, and entrepreneurship.

Against Privacy Fundamentalism in the United States
The article argues against an absolutist view of privacy and advocates for a balanced approach that recognizes the legitimate needs of government and society to access certain information, while still maintaining strong protections for individual privacy rights.

US adults are skipping parenting, having fewer kids, forcing schools to close
The article discusses the declining U.S. birthrate and its impact on schools, as many are being forced to close due to decreased enrollment. Demographic shifts and economic factors are cited as contributing to the lower birthrate, leading to challenges for schools and communities.
The unwritten laws of software engineering
The article explores the unwritten, informal 'laws' that govern effective software engineering practices, such as the importance of communication, the need for continuous learning, and the value of mentorship and collaboration within engineering teams.
Memory Allocation Strategies
The article explores various memory allocation strategies, including stack, heap, and static memory allocation, discussing their characteristics, strengths, and use cases in software development.

Show HN: SpeakStamp – Extension for voice comments on YouTube
Hey, I created this extension to help people make comments in videos with time stamps.

Your Startup Is Probably Dead on Arrival
The article discusses the common reasons why many startups fail, including unrealistic expectations, poor market validation, lack of a viable business model, and insufficient funding. It emphasizes the importance of thorough market research, realistic planning, and addressing key challenges to improve a startup's chances of success.

As student enrollment declines, a look at public school closures
This article tracks the closure of public schools across the United States due to declining enrollment, with many districts struggling to maintain staffing and budgets in the face of these enrollment drops.
Cal Newport: The original attention crisis
The article explores the historical roots of the modern attention crisis, tracing it back to the late 19th century when new technologies and social changes led to the emergence of distracted and fragmented attention spans. It suggests that understanding the historical context can provide insights into addressing the attention challenges faced today.

Show HN: Clawdown – Markdown to PDF with MCP and a pixel cat judging your docs
Clawdown is a new app that enables users to easily manage and download their social media content, including posts, photos, and videos, from various platforms in a secure and organized manner.
I built a launch platform with TanStack Start and Cloudflare Workers in 9 days
'A rocket ship.' AI is doubling software output, and code quality is holding up
The article discusses the rapid growth of AI-powered code generation, leading to a boom in software production but raising concerns about code quality and job displacement for software developers.
Amazon rolls out 1-hour, 3-hour delivery as ultrafast shipping trend grows
Amazon is testing new one-hour and three-hour delivery options in select markets, further expanding its fast shipping capabilities to compete with other e-commerce platforms and meet customer demand for quicker deliveries.

Show HN: Oh-my-agent – A structural harness for AI agents in real projects
If you ask an AI agent to build a todo app, it will usually produce something. But in a real development environment, limitations become obvious: hallucinations, drifting off task, or repeating the same mistakes.
Looking at current prompts and skills, a few recurring problems show up: missing critical library versions, vague personas like you are a senior engineer, and bloated prompts that burn tokens without improving outcomes.
oh-my-agent addresses this by introducing a structured protocol to keep agents aligned with real project constraints.
Key Ideas: 1. Clarification protocol: Analyzes requirement ambiguity to decide whether to proceed, offer options, or stop for clarification.
2. Difficulty guide: Adjusts protocol depth based on task complexity.
3. Context budget: Enforces token limits per model to prevent unnecessary usage.
OpenAI’s Symphony release this March reinforced the importance of this approach. Symphony is powerful for autonomous workflows, but it performs best when the codebase is designed to be AI-friendly.
OpenAI refers to this as harness engineering: structured documentation like ARCHITECTURE.md, AGENTS.md, and WORKFLOW.md that agents can reliably interpret. oh-my-agent is built around these principles. Instead of just sending prompts, it provides the structural harness agents need to understand project context and operate autonomously.
Currently supports: Antigravity, Claude Code, Codex CLI, and Cursor.
The core idea: Using AI agents effectively isn’t about clever prompts—it’s about the engineering structure around them.
"Why do we care about numbers? Numbers make me mad"
The article explores the human fascination with numbers, arguing that our obsession with quantifying and measuring everything can lead to frustration and a distorted perception of reality. It suggests that we should be more mindful of the limitations of numerical data and focus on the qualitative aspects of life.

The Agentic Artisan
The article discusses the concept of the 'agentic artisan', which refers to individuals who take an active role in shaping their work and profession. It explores how these artisans leverage technology and digital tools to enhance their creative autonomy and control over their work processes.
Making Emacs output true 24-bit color in the terminal: a two-line terminfo fix
This article discusses how to configure Emacs to output true 24-bit color in the terminal, improving the visual quality of the text editor.
Show HN: MCP Isn't Dead. You're Just Using It Wrong
Everyone and their gran have been saying that MCP is dead.
But could it be that MCP's saving grace has been with us all along - hiding in plain sight?
A feature buried in Claude Code's Jan 2026 release may have marked the most powerful development in MCP since its inception - and almost nobody noticed. Dynamic Tool Registration.
Dynamic tool registration extends an MCP server's abilities beyond that of just a glorified swagger doc - allowing the server not just to list a static set of tools, but to dynamically add and remove new tools in real time as part of a stateful agent session.
And what's so powerful about that? Well for one it elegantly solves the main problem most people had with MCP in the first place - context bloat. Group your tools into collections of related actions - call them abilities - then provide a load_ability tool. The agent loads what it needs, when it needs it.
But it gets deeper than that.
Last weekend I built and shipped Commandable MCP - the MCP server for creating new MCP servers on the fly. MCP inception, if you will.
It gives agents tools to create new tools, usable immediately without compiling any code or restarting any processes.
Why would I want this?
Think about a standard Trello MCP server. It gives an agent something like create_trello_card(boardId, listId, name, description, labelIds, ...). Every time the agent wants to use it, it has to go fishing for IDs - calling get_boards, get_lists, get_labels - just to find the right place to add the card.
Imagine instead, the agent inspects your actual Trello account and generates add_bug_to_sprint(title, priority) - a tool that already knows your board, your list, your labels. Now it can use that tool whenever it needs to add a bug without reinventing the wheel.
Commandable lets agents build targeted tools for repeatable actions they actually use instead of long lists of generic tools from a standardised MCP or API. Credentials are encrypted at rest and never exposed to the LLM.
And - there's no context bloat. yay.
So, is MCP dead? Not yet.
GitHub: https://github.com/commandable/commandable-mcp
Full writeup: https://commandable.ai/blog/mcp-isnt-dead